In our last benchmarking post, Clarity in complexity: New insights for transparent email security,1 we shared why transparency matters more than ever in email security and how clear, consistent benchmarking helps security teams cut through noise and make confident decisions.
Today, we’re continuing that conversation. With the latest Microsoft benchmarking data, we’re sharing what real-world telemetry reveals about how effectively modern email threats are detected, mitigated, and stopped by Microsoft Defender, secure email gateway (SEG) providers, and integrated cloud email security (ICES) solutions.

This is part of our ongoing commitment to openness: regularly publishing performance data so customers can see how protections perform at scale.
What’s new in the latest benchmarking data
The newest benchmarking results reflect updated telemetry across recent months and reinforce several consistent trends:
Microsoft Defender removes an average of 70.8% of malicious email post-delivery, helping reduce dwell time even when cyberthreats bypass initial filtering.
Layered protection matters. When Defender operates alongside ICES partners, organizations benefit from incremental detection gains across promotional, spam, and malicious messages.
Overlapping detections remain, meaning ICES solutions can flag the same messages and the incremental value-add can vary by scenario and email type.
This kind of data-driven visibility is critical for security teams who want to understand not just whether cyberthreats are blocked, but how and where defenses are adding value across the email attack lifecycle.
Benchmarking results for ICES vendors
Microsoft’s quarterly analysis shows that layering ICES solutions with Microsoft Defender continue to provide a benefit in reducing marketing and bulk email, improving their filtering by an average of 13.7%. This reduces inbox clutter and boosts user productivity in environments with high volumes of promotional email. For filtering of spam and malicious messages, the incremental gains remain modest, and the latest quarter shows a smaller uplift than the prior period—averaging 0.29% and 0.24% respectively, compared to 1.65% and 0.5% in the prior report.
Figure 1. ICES vendor catch contribution (November 2025-January 2026).
Focusing only on malicious messages that reached the inbox, the latest quarter shows Microsoft Defender’s zero hour auto purge performing the majority of post‑delivery remediation—removing an average of 70.8% of these threats. ICES vendors provided additional post‑delivery filtering, contributing an average of 29.2%. Together, this highlights two points: post‑delivery remediation is a critical backstop when cyberthreats evade initial filtering, and in these results Microsoft Defender delivered most of the post‑delivery catch, while ICES vendors add incremental coverage in this scenario.
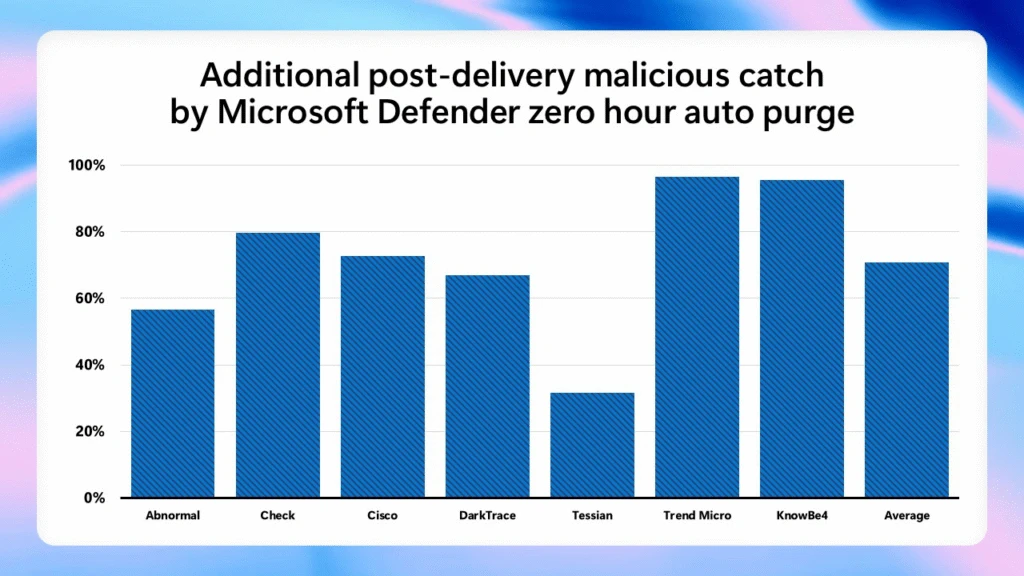
Figure 2. Post‑delivery malicious catch by Microsoft Defender (November 2025-January 2026), shown across vendors and overall average.
Benchmarking results for SEG vendors
For the SEG vendor benchmarking metrics, a cyberthreat was classified as “missed” if it was not detected prior to delivery. Using this definition, Microsoft Defender missed fewer high-severity cyberthreats than other solutions evaluated in the study, consistent with patterns observed in our prior benchmarking report.
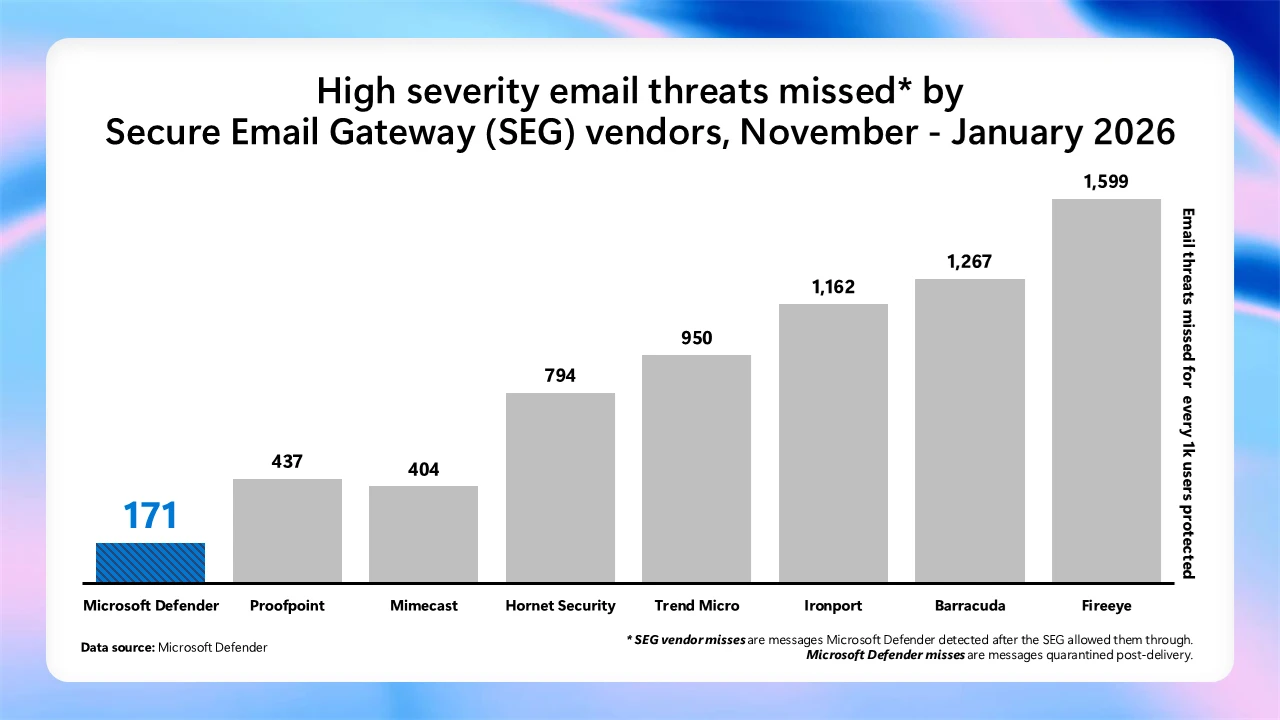
Figure 3. High-severity email threats missed by SEG vendors (November 2025-January 2026), measured as cyberthreats missed per 1,000 users protected.
Reinforcing our commitment to the ICES vendor ecosystem
Transparency doesn’t stop at Microsoft’s own detections. It also extends to how we work with partners.
When we introduced the Microsoft Defender for Office 365 ICES vendor ecosystemour goal was clear: enable customers to integrate trusted, non-Microsoft email security solutions into a unified Defender experience, without fragmenting workflows or visibility.
That commitment continues today.
The ICES vendor ecosystem now includes four partners—Darktrace, KnowBe4, Cisco, and VIPRE Security Group—all integrated directly into Microsoft Defender across experiences such as Quarantine, Explorer, email entity pages, advanced hunting, and reporting.
Customers retain a single operational plane in the Defender portal, even when layering multiple email security technologies.
Integrations are deliberate and additive, designed to enhance protection and clarity without increasing operational complexity.
The ecosystem supports defense-in-depth strategies while preserving a single, coherent security experience.
The recent additions reinforce our belief that email security is strongest when it combines native platform intelligence with specialized partner capabilities, surfaced through a single pane of glass.
We continue to actively evaluate additional partnerships based on customer demand, detection quality, and the ability to deliver meaningful, differentiated signals.
Why this matters for security teams
Email remains one of the most targeted and exploited attack vectors, and modern campaigns rarely rely on a single technique or control gap.
By pairing transparent benchmarking with integrated, multi-vendor protection, security teams gain:
Clear insight into detection coverage across native and partner solutions.
Reduced investigation friction with unified views and workflows.
Confidence in layered defenses, backed by regularly published data.
This isn’t about claiming perfection. It’s about showing the work, sharing the numbers, and giving customers the information they need to make informed security decisions.
Looking ahead
We’ll continue to publish updated benchmarking insights on a regular basis, alongside ongoing investments in Microsoft Defender and the ICES vendor ecosystem.
To explore the latest benchmarking data and learn more about how Defender and ICES partners work together, access the benchmarking site.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and X (@MSFTSecurity) for the latest news and updates on cybersecurity.
1Clarity in complexity: New insights for transparent email security, Microsoft. December 10, 2025.




GIPHY App Key not set. Please check settings